Intrepid V6-2.7L VIN R (2003)
Alarm Module: Description and Operation
SENTRY KEY IMMOBILIZER MODULE
Sentry Key Immobilizer Module
The Sentry Key Immobilizer Module (SKIM) (Fig.10) contains a Radio Frequency (RF) transceiver and a central processing unit, which includes
the Sentry Key Immobilizer System (SKIS) program logic. The SKIS programming enables the SKIM to program and retain in memory the codes
of at least two, but no more than eight electronically coded Sentry Key transponders. The SKIS programming also enables the SKIM to
communicate over the Programmable Communication Interface (PCI) bus network with the Powertrain Control Module (PCM), and/or the DRB
III scan tool.
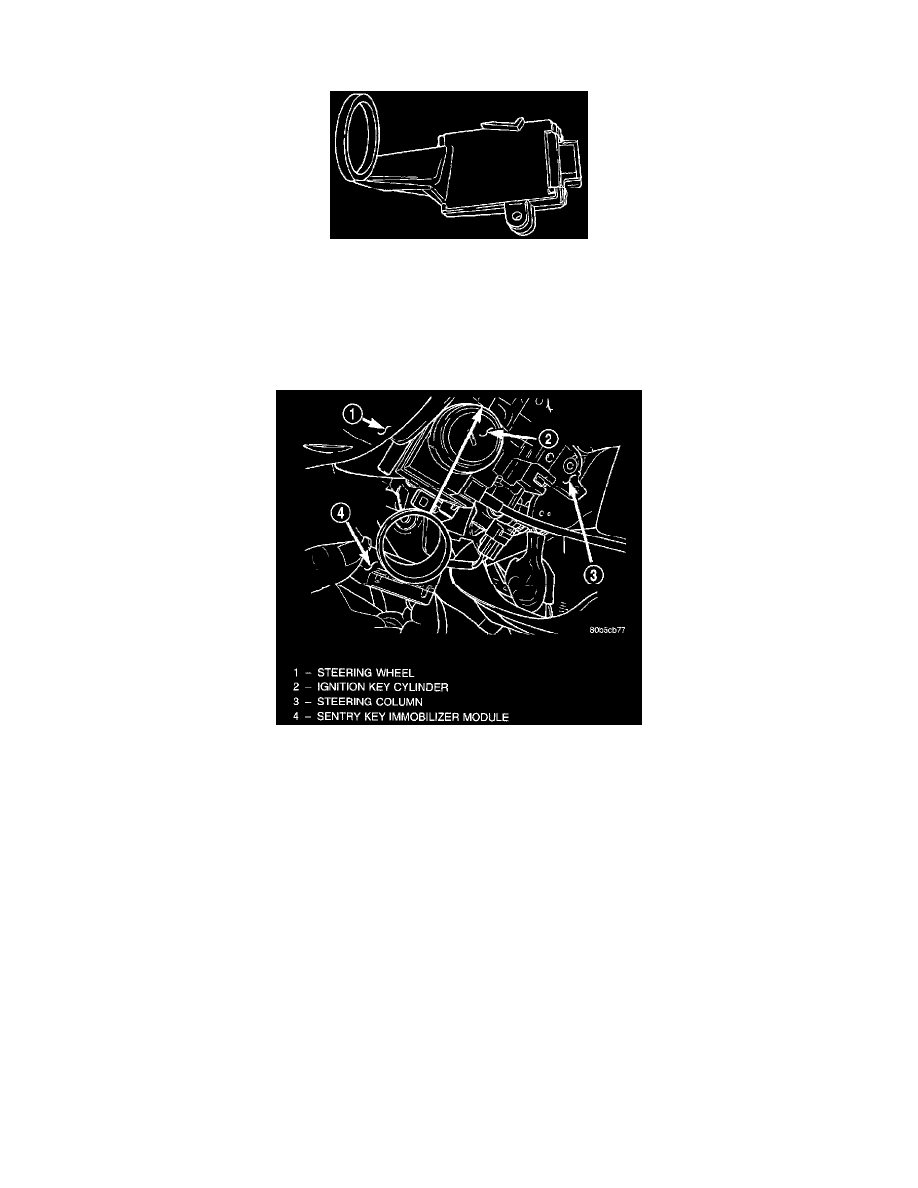
Sentry Key Immobilizer Module Location
The SKIM transmits and receives RF signals through a tuned antenna enclosed within a molded plastic ring formation that is integral to the SKIM
housing. When the SKIM is properly installed on the steering column, the antenna ring is oriented around the circumference of the ignition lock
cylinder housing. This antenna ring must be located within eight millimeters (0.31 inches) of the Sentry Key in order to ensure proper RF
communication between the SKIM and the Sentry Key transponder.
For added system security each SKIM is programmed with a unique "Secret Key" code and a security code. The SKIM keeps the "Secret Key"
code in memory and sends the code over the PCI bus to the PCM, which also keeps this code in its memory. The SKIM also sends the "Secret
Key" code to each of the programmed Sentry Key transponders. The security code is used by the assembly plant to access the SKIS for
initialization, or by the dealer technician to access the system for service. The SKIM also stores in its memory the Vehicle Identification Number
(VIN), which it learns through a PCI bus message from the PCM during initialization.
The SKIM and the PCM both use software that includes a rolling code algorithm strategy, which helps to reduce the possibility of unauthorized
SKIS disarming. The rolling code algorithm ensures security by preventing an override of the SKIS through the unauthorized substitution of the
SKIM or the PCM. However, the use of this strategy also means that replacement of either the SKIM or the PCM units will require a system
initialization procedure to restore system operation.
When the ignition switch is turned to the ON or START positions, the SKIM transmits an RF signal to excite the Sentry Key transponder. The
SKIM then listens for a return RF signal from the transponder of the Sentry Key that is inserted in the ignition lock cylinder. If the SKIM receives
an RF signal with valid "Secret Key" and transponder identification codes, the SKIM sends a "valid key" message to the PCM over the PCI bus. If
the SKIM receives an invalid RF signal or no response, it sends "invalid key" messages to the PCM. The PCM will enable or disable engine
operation based upon the status of the SKIM messages.
